Stolen credentials are involved in 80% of breaches. Stop worrying about passwords forever.
Stolen credentials are involved in 80% of breaches. Stop worrying about passwords forever.
Stop Worrying About Passwords Forever.
How Does Scirge Pevent Passwor-related Threats Forever?

The Scirge browser extension can detect any web form such as logins, registrations, or any other credential submission using centrally-managed policies. All submissions are monitored including on phishing sites and unknown services.
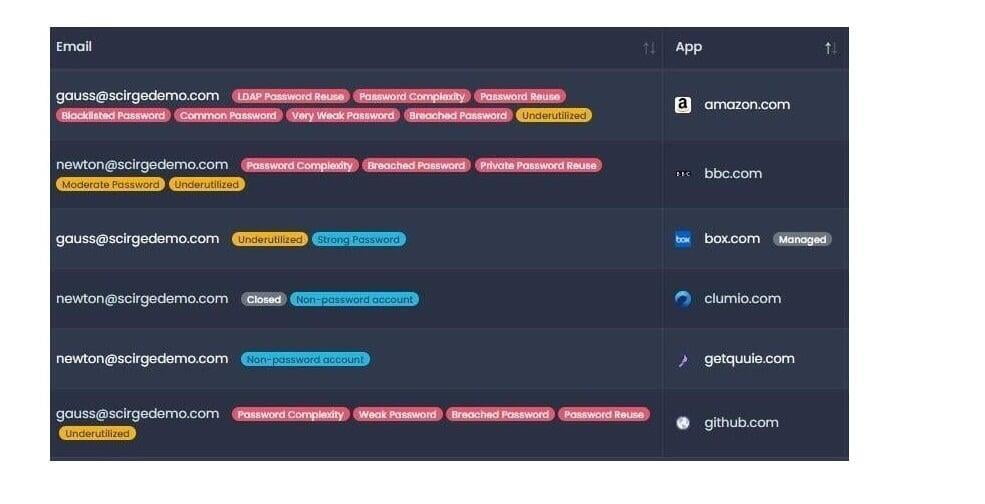
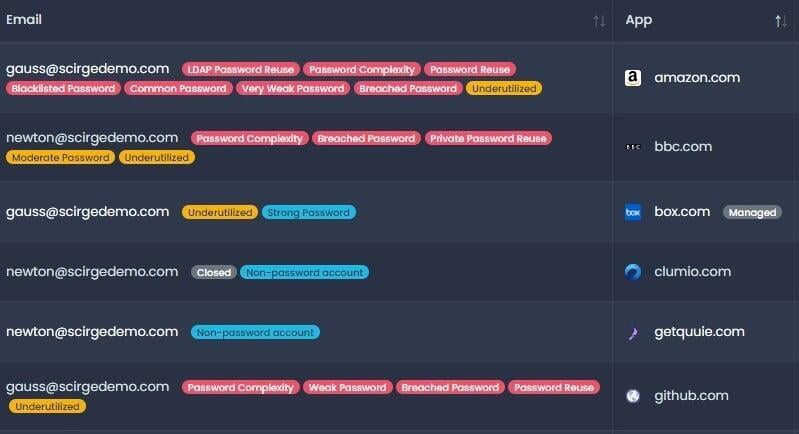
A typical policy is to monitor the usage of all corporate-related email domains. Each password used is checked for strength and complexity without any user interaction.

When any user submits corporate credentials through the browser, Scirge Endpoint Browser Extension will report it to the Central Server for correlation. This server runs in your local environment for maximum privacy and security.
Only the secure hashes of passwords are collected, so passwords can not be compromised from the network traffic or even by local administrators.
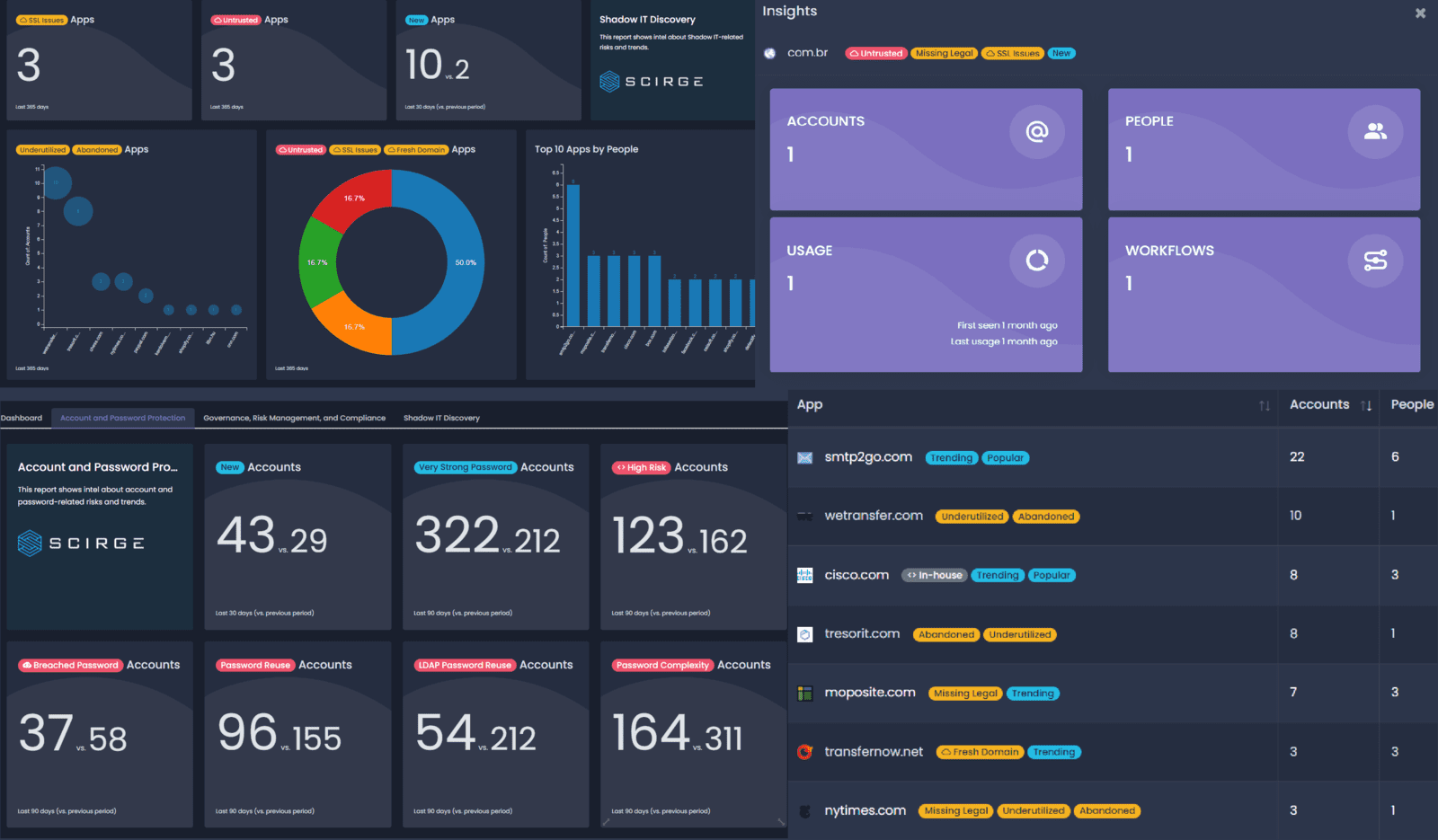
Automations are triggered to warn employees about risky passwords, accounts, and applications, trigger Syslog or API-based workflows such as an LDAP reset, or notify administrators about high-priority events. All of the data can be visualized using flexible reporting capabilities for each separate stakeholder and department.
Additionally, Instant Discovery can be run to detect browser-saved passwords to prevent unsecure storage and unmanaged synchronization of corporate accounts and passwords.
Features
Scirge provides a unique approach to unveil and gain control over unmanaged third-party web accounts. Scirge tracks the websites employees use corporate email addresses to register on and log in to.
App and Account Discovery
Password Hygiene
Education
and Automation
Use Cases
Visibility for cloud apps means control over your supply chain. Manage your Enterprise Attack Surface through automation and education. Discover legacy applications, accounts, and internal threats via application and account inventories.
Create inventories for Zero Trust efforts, Data Processors, Identity Management, and Business Continuity.
No matter your regulations, managing your inventories and external assets is fundamental for compliance.
Detect phishing attacks, breached or reused LDAP and third-party passwords, weak credentials, and unmanaged accounts. Scirge provides the highest level of password hygiene because it doesn't rely upon any opt-in action from employees –it's completely transparent.
Can you recall what websites did you register on with your corporate email address this year? Last year? Or the year before?
Each person has 200 online accounts on average.
Online accounts are created by employees daily for various business needs. Mostly on-demand and in an ad-hoc way. This can result in thousands of unmonitored accounts, creating an enormous amount of risks and compliance issues.
This is what's called Shadow IT.
Discover Browser-Saved Accounts and Application Usage
Watch our Webinar!
© 2022 Scirge.com, All rights reserved. www.scirge.com/privacy